7 best practices to follow to avoid a data breach

IBM reported that the cost of a data breach reached $4.35 million in the year 2022. Moreover, on average, it took 277 days to identify and contain the breach. 83% of the surveyed organizations reported that they were breached more than once.
Data breaches can be costly and take a toll on the reputation and profitability of the organization. Therefore, they must be avoided at all costs. So, let us learn about seven best practices to follow to avoid a data breach.
What is a data breach?
A data breach is an incident where cybercriminals access the data/information in an unauthorized manner to use it for malicious purposes. A data breach can cost an organization money, time, effort, and even reputation. Customers lose trust if the organization they are dealing with falls victim to a data breach.
The following chart shows the rising cost of data breaches over the years.

Best practices to follow to avoid a data breach
Cybersecurity policies and compliances do not guarantee that your organization will not be breached. Every organization must be well prepared for data breaches. As they say, “Hope for the best, prepare for the worst." Here are some of the steps you can take to avoid a data breach.
Perform risk assessment
Risk assessment in information security refers to the steps taken to identify, detect, analyze, and evaluate the risks that your organization faces. You must know your strengths and weaknesses for a thorough risk assessment.
Risks come in different forms; for example, if you know that your employees are susceptible to clicking on phishing links or there are a number of disgruntled employees who might use a chance to get back at you. If you are taking over a company, it might come with its own risks. Therefore, risk assessment is a step you cannot miss.
Implement a robust incident response plan
IBM also reported that 23% of the organizations still lacked an incident response plan. Only 63% of the organizations that had a plan tested it periodically.
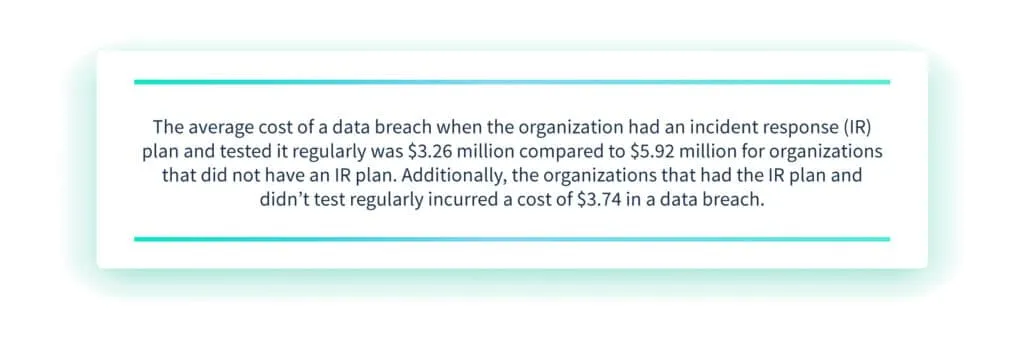
The above chart clearly depicts that having an incident response plan and testing it regularly can lower the cost of a data breach.
An incident response plan is a process that is designed to follow when your organization's systems are breached. Every organization must have a solid incident response plan in place from the very beginning. This plan should be verified periodically to ensure that it is up to date. It should be communicated to all employees to ensure that they follow the steps addressed in the plan.
Some of the information to be included in the incident response plan are:
- Procedures to be observed by the first person to observe the incident
- Procedures to be followed by the damage assessment team (DAT)
- Reporting policies to the regional incident manager and the threat assessment center
- Activation of emergency operations center (EOC)
Strengthen threat intelligence
Threat intelligence refers to an organization's efforts to identify and detect potential threats to its information systems. Cybercriminals are always on the lookout for vulnerabilities in popular software that they can exploit. Once they discover this vulnerability, they will fashion different ways to exploit it.
Before the software developer knows, the criminals reach the users of the software and steal their information. As soon as the developer realize their vulnerabilities, they start working on developing and then releasing patches to cover those vulnerabilities. These types of attacks are called zero-day attacks; for instance,
- CISA warned of Windows and iOS bugs exploited as zero-day
- Microsoft patched 77 flaws exploited as zero-day in February 2023
- Apple fixed a new Web-kit zero-day exploited to hack iPhones and Mac
An organization must watch out for the threats in the industry to protect itself better. It's critical for cybersecurity that the organization stays on top of the security news and updates its software as soon as the developer releases the patches.

Instead of being reactive, you must be proactive and stay in touch with your security consultant, who can guide you to stay at the top of your game.
Conduct regular training and simulation
According to Hornet Security's data, 1 in 3 organizations (33%) do not provide any cybersecurity training to its remote employees despite 74% of them having access to critical information. IBM reported that employee training could save $247,758 in case of a data breach. Despite huge savings, a third of companies refrained from training their employees.
Training should include

Carry out detection and analysis
Extended detection and response (XDR) is a threat detection technique that correlates data over multiple platforms, including email, endpoints, server, network, and cloud workloads. Organizations with robust XDR can save 29 days in the detection and containment of a data breach (IBM). IBM also reported that organizations with XDR technologies saved $190,622 in the cost of a data breach. However, XDR techniques are applied by only 44% of organizations.
Some of the ways of detecting a data breach are as follows:
- Newly installed programs
- Strange traffic on the network
- Failure to log in with authentic username and passwords
- Unusual data access
- Unusual outbound traffic
- Log tampering
When you detect an intruder earlier in the breach, you can prevent them from accessing a larger amount of data.
The analysis involves verifying how much organization information is stolen by the breach and which databases are affected. As soon as you realize there is a breach, your IT department, together with your security partners, must identify the affected areas and quarantine them to stop the spread of the attack.
Bring in the experts
When you face a data breach, your IT department might not be sufficient to reverse engineer the attack and rebuild the organization's systems. You can bring in cybersecurity partners that can help you respond to the breach systematically and on time. It can give the organization a bird's eye view of the situation and help reduce downtime.
An organization that is hacked needs to inform its stakeholders and regulatory bodies as soon as they know the extent of the damage done. If your IT department has some help, they can carry out the procedures effectively. To prepare for emergencies like a data breach, an organization must have a clear plan of who to involve and when.
Prepare a containment and eradication plan
The containment and eradication plan is dependent on the analytics provided by security experts. Containment refers to stopping the spread of cyber attacks on the assets not yet affected. After limiting the cyber attack's impact, the security experts move towards eradication. Eradication is the process of removing any traces of attackers from the organization's networks.
The next step is to identify the vulnerabilities in the organization's systems and patch them to avoid another attack. It is after the security experts are certain that the attackers are not in the system and the vulnerabilities are sealed off that they begin the process of recovery, where they retake control of compromised assets.
Final thoughts
Although an organization's efforts should be aligned with security, preparing for the worst situation can make the response attempts more effective. We saw seven best practices to follow in preparation for a data breach. If an organization is prepared to fight unfavorable circumstances, the loss of time and money can be minimized.
A data breach can not only ruin your reputation but also slow down your progress. You might lose business opportunities and customers. Therefore, it is imperative that you prevent data breaches with all your might. To learn more about how Scrut can help you, click here.
FAQs
What is an incident report plan? An incident report plan is designed to list the policies and procedures to be followed in case there is a security incident in the organization.
What are the steps to follow to prepare for a data breach? The following steps should be followed to prepare for a data breach:
1. Risk assessment
2. Incident response plan
3. Threat intelligence
4. Training and simulation
5. Detection and analysis
6. Bring in the experts
7. Containment and eradication
What is threat intelligence? Threat intelligence is collecting, analyzing, and processing knowledge and information about the threats that can affect the organization.


















