When most people hear “PCI DSS,” they picture big banks, payment processors, or retail giants with dozens of stores. But here’s the reality— if your business touches credit or debit card data in any way, you’re already in PCI DSS territory.
The Payment Card Industry Data Security Standard (PCI DSS) isn’t just another checkbox. It’s a global standard designed to protect cardholder data and reduce the risk of payment fraud. And with data breaches growing in scale and sophistication, PCI DSS compliance has become a trust signal for businesses of all sizes.
So who exactly needs PCI DSS? This blog will help you cut through the jargon and figure out if — and how — the standard applies to your business. Whether you’re a SaaS startup, a growing e-commerce brand, or a service provider supporting payment workflows, we’ll walk you through what matters and why.
What is PCI DSS?
PCI DSS stands for Payment Card Industry Data Security Standard — a global benchmark for securing credit and debit card transactions. It was developed by the PCI Security Standards Council, a group made up of major card brands like Visa, Mastercard, American Express, Discover, and JCB.
The standard is all about protecting cardholder data — meaning, it applies only if your systems store, process, or transmit information from payment cards. If your customers pay using UPI, ACH, crypto, or digital wallets without touching card networks, PCI DSS doesn’t directly apply. But if those wallets are funded by cards — or if your systems ever see or touch the card number — you’re still on the hook.
PCI DSS lays out 12 security requirements, grouped into six key objectives, covering everything from network security and encryption to access control and continuous monitoring. Some examples include:
- Installing firewalls and anti-virus software
- Encrypting stored and transmitted cardholder data
- Restricting access to card data based on business need
- Maintaining secure systems and conducting regular testing
While it’s not a government regulation, PCI DSS is contractually enforced by payment processors and card brands. In most cases, failing to comply means fines, penalties, increased transaction fees— or even losing the ability to accept card payments.
So if you’re working with card data in any way, PCI DSS isn’t optional — it’s foundational.
Who must comply with PCI DSS?
PCI DSS isn’t just for banks or payment processors — it’s for any business that accepts, stores, or transmits cardholder data. That includes everything from global retail brands to your favorite neighborhood café that uses a card reader at checkout.
Let’s break down the main groups who fall squarely under PCI DSS requirements:
1. Merchants
If your business accepts credit or debit card payments — online, in-store, or via mobile apps — you’re a merchant in the eyes of the PCI Security Standards Council. And that means PCI DSS applies to you.
You could be:
- A solo founder running an e-commerce store
- A chain of restaurants accepting card swipes
- A mobile app with integrated card payments
Merchants are classified into four levels based on the annual volume of card transactions. Here’s a quick breakdown of the merchant levels:
- Level 1: Over 6 million transactions per year
- Level 2: 1 million to 6 million transactions per year
- Level 3: 20,000 to 1 million e-commerce transactions per year
- Level 4: Fewer than 20,000 e-commerce transactions (or up to 1 million total across all channels).
2. Service providers
This category includes third-party businesses that store, process, or transmit cardholder data on behalf of other organizations — they’re not charging the card themselves but are still deeply involved in the payment ecosystem.
Common examples:
- Payment gateways
- Cloud service providers that host systems handling cardholder data
- Managed service providers (MSPs) that manage or secure IT systems interacting with card data
Just being in the payment ecosystem isn’t enough to qualify — you’re considered a service provider only if your services involve handling cardholder data on behalf of someone else.
3. SaaS platforms with payment features
If your SaaS product enables other businesses to collect payments — like booking systems, event platforms, or B2B marketplaces — you might fall under PCI DSS, depending on how you handle card data.
Here’s the deal:
- If your platform stores, processes, or transmits cardholder data, PCI DSS definitely applies.
- If you integrate a third-party payment processor (like Stripe or Razorpay) without ever touching card data — not on your front end, back end, or logs — your PCI scope may be limited. But you’re still expected to validate that your payment provider is PCI compliant.
- If your systems “see” or temporarily handle cardholder data (even if just for a split second before handing it off), you’re still in scope and must comply.
In short, even relying on a third party doesn’t give you a free pass — it just changes your responsibilities under PCI DSS.
Is PCI DSS compliance legally required?
Not exactly. PCI DSS isn’t a law — it’s a contractual obligation enforced by credit card brands and payment processors. But if you process card payments and don’t comply, you risk fines, penalties, or even termination of your ability to accept cards.
But there’s more to it. While PCI DSS itself isn’t a law, some jurisdictions have woven its requirements into their legal frameworks. For instance, Nevada state law (NRS 603A) mandates that businesses handling payment card data must comply with the current version of PCI DSS or use security measures that offer equivalent protection. So, depending on where you operate, PCI DSS compliance might not just be contractual — it could be legally expected too.
Who should consider PCI DSS — even if it’s not mandatory?
Not every business is formally required to comply with PCI DSS — especially if you don’t directly handle cardholder data (say, you’ve fully outsourced payments to a PCI-compliant processor). But in practice, there are several scenarios where voluntary compliance becomes a smart move — if not an outright necessity.
Here’s who should be paying attention:
Startups with growth ambitions
If you’re building a SaaS product or marketplace that might integrate payments down the line, it’s worth thinking about PCI DSS early. Compliance becomes harder (and costlier) to retrofit later. Plus, enterprise customers often ask vendors to demonstrate secure payment handling practices —even if your app doesn’t directly store cardholder data..
PCI DSS is also a green flag during fundraising and enterprise sales — signaling you’re serious about security from day one.
Fintechs and embedded finance players
Fintech companies offering wallets, virtual cards, lending, or Banking-as-a-Service (BaaS) often sit in a gray zone when it comes to cardholder data. Even if you’re not directly processing payments, you might still interact with tokenized or encrypted cardholder data through partner APIs — and that can bring you into PCI DSS scope.
You may need to comply due to:
- Partner agreements with acquiring banks or payment processors
- Vendor due diligence when integrating with major card networks
- Regulatory or customer expectations in highly scrutinized sectors like finance and lending
- Contractual obligations, especially if your company provides white-labeled payment solutions or BaaS offerings
In fact, many payment processors require fintech partners to demonstrate PCI DSS readiness, regardless of their direct technical role.
B2B vendors in the payment ecosystem
If your product supports businesses that accept card payments — say, an invoicing tool, fraud detection engine, or checkout optimization API — your customers might require you to be PCI-compliant before plugging into their stack. It becomes part of the trust equation, especially for larger merchants or regulated industries.
Businesses expanding globally
Different regions have different expectations. If you’re moving into North America or Europe, enterprise customers may demand PCI compliance as a precondition — even if you’re using Stripe or another third-party processor. You don’t want compliance to be the thing holding back your go-to market efforts.
A checklist — Who needs PCI DSS compliance?
Not sure whether PCI DSS is your responsibility? Here’s a quick self-check. If you answer “yes” to even one of these, you’re likely in scope:
- Do you accept credit or debit card payments, online or offline?
- Does your business store, process, or transmit cardholder data — even briefly?
- Do you use a payment gateway, POS terminal, or any system that interacts with card payments?
- Are you a service provider supporting other businesses’ payment infrastructure?
- Does your app or platform let customers enter card details in any form?
- Do you build tools or integrations for merchants who handle payments?
- Are you entering a partnership, contract, or market that requires PCI compliance?
If any of these sound like your business, PCI DSS is either already on your radar — or it should be.
Still unsure whether PCI DSS compliance is right for your business? Our Compliance Finder can help you figure it out.
How to get started with PCI DSS compliance
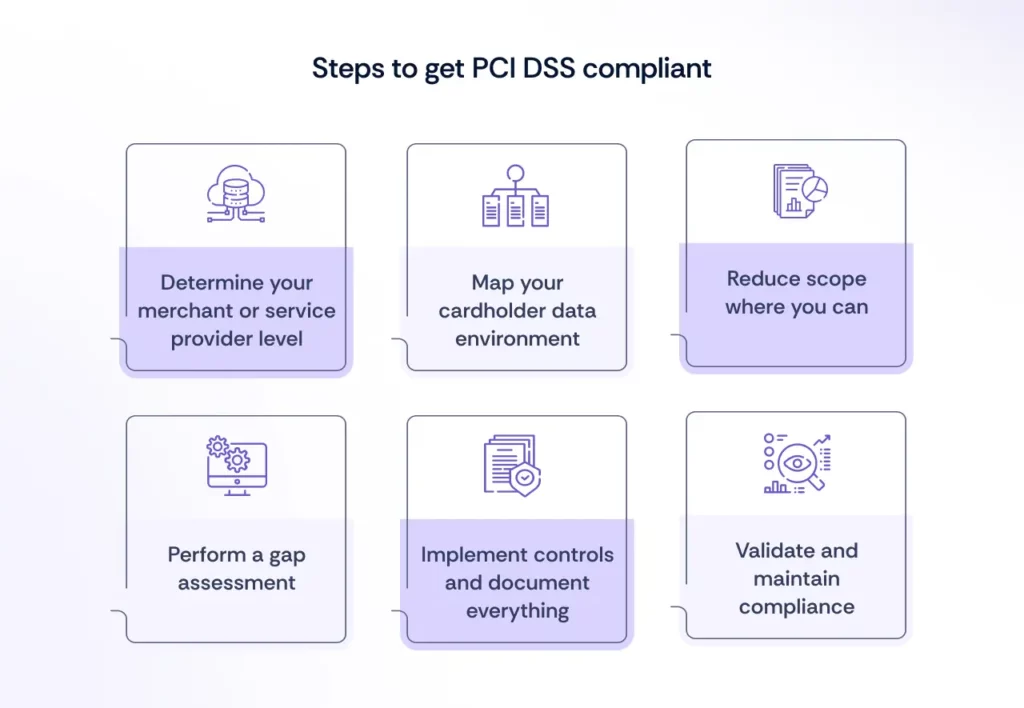
If PCI DSS feels overwhelming, you’re not alone. But the path forward doesn’t have to be a guessing game. Here’s a practical way to kick things off:
1. Determine your merchant or service provider level
PCI DSS breaks down compliance requirements based on how many card transactions your business handles annually. This classification helps decide whether you can self-assess or need a formal audit by a Qualified Security Assessor (QSA).
- Level 1: Requires an annual QSA audit and detailed reporting
- Level 2: May require a Self-Assessment Questionnaire (SAQ) and quarterly scans
- Level 3: Typically eligible for SAQ and scan validation
- Level 4: May require only an SAQ, depending on your acquirer’s requirements
If you’re a service provider (i.e., you process payments on behalf of others), different thresholds apply — but the general rule still holds: higher transaction volume means tighter scrutiny.
Knowing your level helps you understand your validation path and how much effort will be required upfront.
2. Map your cardholder data environment
This is your scoping step. Identify where cardholder data is:
- Accepted (e.g. web forms, POS systems)
- Transmitted (e.g. APIs, payment gateways)
- Stored (e.g. logs, databases, temporary caches)
Don’t forget indirect exposure — like browser sessions or third-party scripts.
3. Reduce scope where you can
Not all systems need to be in PCI scope. If possible:
- Tokenize or encrypt card data at the point of entry
- Use a PCI-compliant payment processor to outsource collection
- Avoid storing card data unless absolutely necessary
Smaller scope = lower risk = easier compliance.
4. Perform a gap assessment
Compare your current controls against the PCI DSS requirements. This is where many teams discover:
- Missing documentation
- Insecure configurations
- Gaps in access control or monitoring
Knowing where you stand helps prioritize fixes.
5. Implement controls and document everything
PCI DSS places heavy emphasis on:
- Written policies and procedures
- Regular testing (e.g. vulnerability scans)
- Ongoing training for staff
Even if your tech is locked down, a lack of documentation can be a blocker.
6. Validate and maintain compliance
Depending on your merchant level or service provider status, this may mean:
- Completing an SAQ
- Undergoing a formal audit by a QSA (Qualified Security Assessor) (if required)
- Submitting an Attestation of Compliance (AOC)
And remember: compliance is not one-and-done. PCI DSS requires continuous monitoring and periodic assessments.
What are the consequences of non-compliance with PCI DSS?
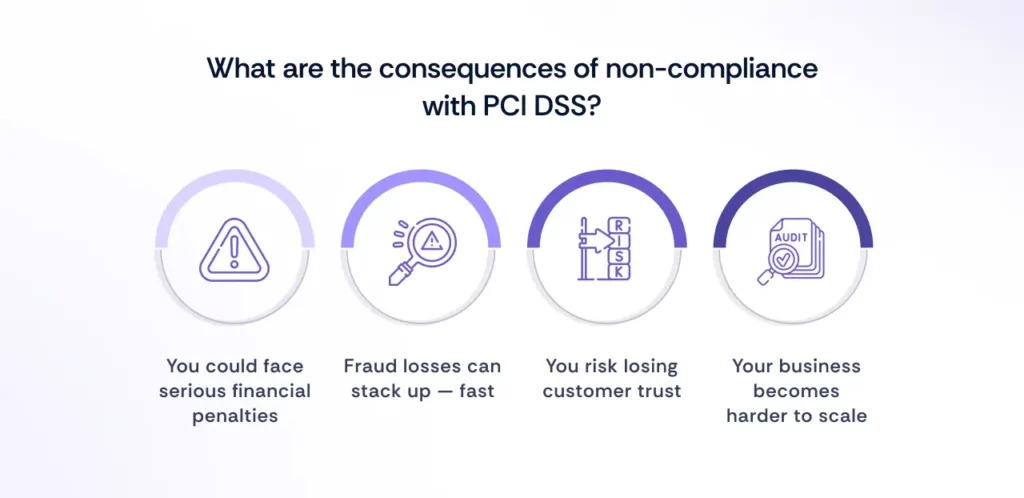
Ignoring PCI DSS compliance isn’t just a technical oversight — it’s a business risk. Here’s what could happen if you operate in the card payment space and don’t meet PCI standards:
You could face serious financial penalties
If you suffer a data breach and aren’t PCI DSS compliant, payment card brands (like Visa or Mastercard) can impose hefty fines. These can range from $5,000 to $100,000 per month, depending on the severity and duration of non-compliance — and that’s on top of breach remediation costs.
Worse, your acquiring bank might terminate your ability to process card payments altogether — which, for most businesses, is a death sentence.
Fraud losses can stack up — fast
According to the 2025 Global eCommerce Payments & Fraud Report, 98% of merchants experienced some form of fraud in the past year. Among those, refund/policy abuse impacted 57%, and real-time payment fraud hit 45% — now the second most common fraud type globally.
PCI DSS was designed to reduce the risk of exactly this kind of fraud. Without it, you’re not just non-compliant — you’re exposed.
You risk losing customer trust
A data breach tied to cardholder data doesn’t just hurt your bottom line — it hits your brand. Rebuilding trust after a card data leak is tough, especially if it becomes public or leads to fraudulent charges.
And let’s be honest: customers expect you to protect their financial information. PCI DSS is the baseline they assume you’re already meeting.
Your business becomes harder to scale
Non-compliance can delay vendor approvals, kill enterprise deals, and limit partnerships with payment processors. As your business grows, the cost of retroactive compliance balloons. Doing it early is far cheaper than doing it under pressure — or after a breach.
Common misconceptions about PCI DSS
Let’s clear the air. Many businesses think they’re off the hook when it comes to PCI DSS — but in reality, the standard applies more broadly than most assume. Here are a few common myths that need retiring:
“We use a third-party processor, so we’re off the hook.”
Not quite. Using Stripe, Square, or any other PCI-compliant processor reduces your PCI DSS scope — but it doesn’t eliminate it. You’re still responsible for how your app or infrastructure interacts with card data, including how you collect it, transmit it, or display it in your UI.
“PCI DSS is only for large enterprises.”
Nope. PCI DSS applies to any organization that handles payment cards — whether you’re doing 50 transactions a year or 50 million. Smaller merchants may have simpler compliance requirements, but they’re still expected to follow the standard.
“We’re secure — we don’t need PCI DSS.”
Security ≠ compliance. You might be following good practices, but unless you’ve formally assessed and documented those controls against PCI DSS requirements, you’re still non-compliant. And if there’s a breach, “we thought we were secure” won’t fly.
“PCI DSS is just another checkbox.”
This one’s dangerous. PCI DSS is based on real attack patterns and fraud risks. It’s not about bureaucracy — it’s about minimizing the chances of becoming a fraud statistic, like the 98% of merchants who were hit last year.
Need help automating PCI DSS compliance?
PCI DSS compliance can feel like a maze — scattered documentation, dozens of technical controls, and never-ending evidence requests. That’s where Scrut comes in.
Scrut is a modern GRC and compliance automation platform purpose-built for cloud-native companies. Whether you’re a fast-moving startup or a scaling enterprise, Scrut helps you take control of PCI DSS (and other frameworks) without the usual compliance chaos.
With Scrut, you can:
- Leverage 1400+ pre-mapped controls — mapped once, reused across frameworks/standards like ISO 27001, SOC 2, and PCI DSS
- Visualize your card data environment and system scope using clear, customizable diagrams
- Assign and track tasks across teams with automated reminders and ownership flows
- Centralize your audit evidence in one place, so you’re not chasing screenshots or stale spreadsheets
- Integrate with your existing stack — including cloud platforms, ticketing tools, and identity providers — to auto-collect evidence where possible
- Get real-time visibility into control status, deadlines, and potential gaps before they become audit blockers
And when you’re ready to validate your compliance? Scrut helps you collaborate with your QSA or assessor through a shared workspace — keeping things efficient, audit-friendly, and transparent.
Ready to simplify PCI DSS?
Let Scrut do the heavy lifting — from control mapping to evidence collection.

FAQs
What counts as “cardholder data”?
Cardholder data includes any information found on a credit or debit card — like the Primary Account Number (PAN), cardholder name, expiration date, and CVV code. If you store, transmit, or process any of these, PCI DSS applies to you.
Do I need PCI DSS if I use Stripe, Square, or another third-party processor?
Yes — but your scope may be reduced. If you never see, touch, or store cardholder data, and the processor handles everything via a hosted payment page or redirect, your compliance obligations are lighter. That said, you’ll likely still need to complete a Self-Assessment Questionnaire (SAQ) and follow secure integration practices.
How often do I need to validate PCI DSS compliance?
That depends on your merchant level. Some businesses need to validate annually via a full audit; others can self-assess. Regardless of the method, compliance is continuous — not just a one-time event.
What’s the difference between PCI DSS and other frameworks like SOC 2 or ISO 27001?
PCI DSS is specifically focused on payment card data, while SOC 2 and ISO 27001 are broader information security frameworks. If your business handles card payments and needs to demonstrate overall security posture, you might need to comply with all three — which is where a unified platform like Scrut can help.

Megha Thakkar has been weaving words and wrangling technical jargon since 2018. With a knack for simplifying cybersecurity, compliance, AI management systems, and regulatory frameworks, she makes the complex sound refreshingly clear. When she’s not crafting content, Megha is busy baking, embroidering, reading, or coaxing her plants to stay alive—because, much like her writing, her garden thrives on patience. Family always comes first in her world, keeping her grounded and inspired.