Does Compliance equal Information Security?

If you’re familiar with the information security domain, chances are you have heard about the LastPass data breach that came to light in August 2022.
In December 2022, the organization admitted to the severity of the breach and revealed they were victims of a data breach when an intruder gained access to their internal development environment. Post this admission, several CISOs and cybersecurity leaders worldwide expressed their opinions on LastPass falling prey to a data breach despite having a ‘clean SOC 2 report.’
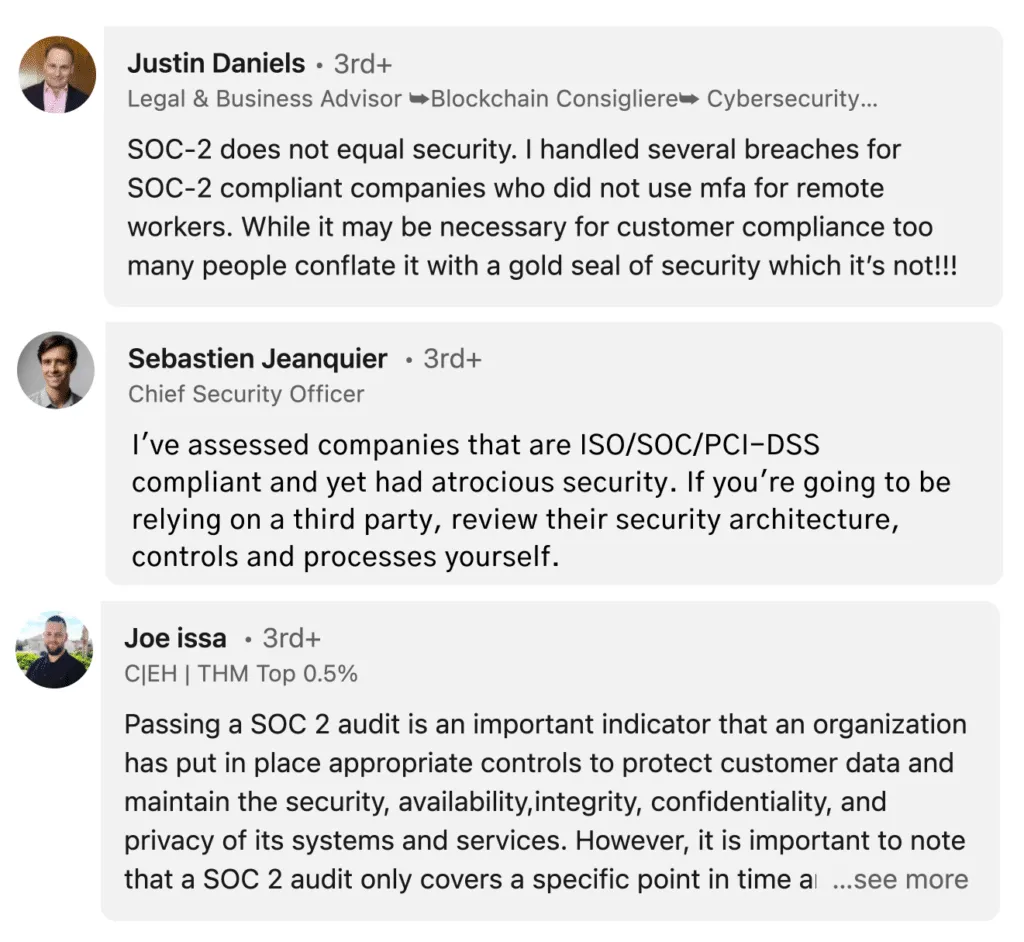
This led to comments about how compliance does not equal information security.
While this statement may hold significant truth, it is essential first to understand why. Let’s do a deep dive into the topic and draw our conclusions.
Why is compliance only the first step toward security?
Compliance, as per definition, means your organization meets the minimum standards for security requirements. Organizations may have to stop their operations if they are not complying with specific frameworks and regulations – depending on their industry.
For instance, if a health provider is not compliant with HIPAA, they might not be able to store, share or access personal health information, bringing their business operations to an immediate halt.

The major reason organizations adhere to these frameworks is to safeguard themselves by implementing the policies and procedures required for a protected digital environment. As a result, achieving, proving, and maintaining compliance is critical.
However, because of this placed importance, many organizations adopt a compliance-first mindset, which instills that all decisions must focus on the frameworks and maintaining compliance.
Let’s learn more about how a compliance-first mindset can restrict information security.
What are the limitations of compliance in cybersecurity?
While compliance is critical for operations, a compliance-first approach can be exceedingly restricted, slow, and inflexible. It can force any other security initiatives on the back burner.
For instance, here are a few ways a compliance-first mindset can limit the organization’s security.
- Organizations spend a lot of time and resources implementing compliance frameworks from the ground up. A major drawback of this approach is the repetitive ‘threat-compliance-framework’ cycle. It means by the time the framework is released; it is already out of context with the most recent threats. Until these threats are eventually covered with updated frameworks, new threats surface.
- Regulatory frameworks are frequently viewed as tick boxes by organizations with a compliance-first approach. This framework-first approach ignores the fact that each organization has a unique user base and technological stack. They may operate in the same section but are fundamentally distinct and require additional protection when obtaining, proving, and maintaining compliance.

This is where a security-first mindset comes into play. A security-first approach is concerned with achieving the highest feasible security posture for a company while remaining within the constraints of its business operations and finances.
For instance, under SOC 2 compliance, organizations are required to implement access management. For a small company with 5-10 employees, a regular monthly review with fewer transitions might be sufficient. But against an organization with 500 employees, the same monthly review would no longer serve its purpose. In these cases, a security-first approach will require you to use tools like Zluri or Blissfully for access management.
This isn’t to imply that a compliance-first approach is derogatory. It simply lacks the steps that a security-first approach would necessitate, such as authenticating user credentials via identity management procedures that entail more than just a login and password.
How can you close the gap between cybersecurity and compliance?
As mentioned earlier, compliance is only the first step toward information security. It provides organizations with protection against regulatory risk.
However, organizations are duly exposed to other risks because of business continuity, operations, employees, and brand identity, each of which can directly translate into financial damage and is not covered by compliance frameworks.
Does that mean that organizations should stop focusing on maintaining compliance with frameworks?
Not quite.
Compliance frameworks and regulations will not stop holding importance; in fact, several new regulations are coming to fruition, such as Digital Personal Data Protection Bill, Personal Data Protection Law, and California Privacy Rights Act – which will redefine the way organizations protect customer’s data.
However, that also doesn’t imply our approach toward achieving compliance needs to stay the same.
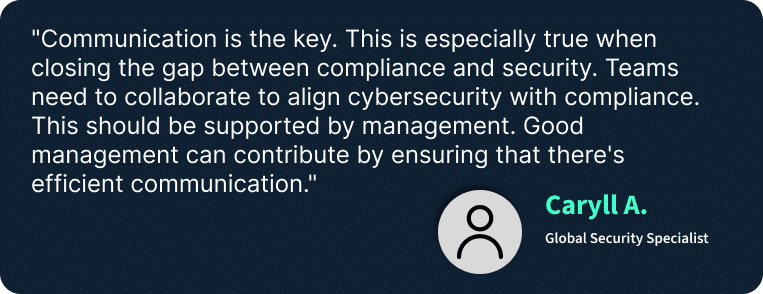
You can begin to combine your organization’s security posture and compliance needs by including additional security considerations into your decision-making processes and not letting compliance take the rein. This results in a more organic method of obtaining compliance while also improving your security posture.
Moving forward with the three I’s – Implementation, Investigation, and Improvement
Bridging the gap between compliance and information security is not something organizations can do overnight. In order to take the right steps toward maintaining compliance and security, there are some practices that they will be required to follow.
We have streamlined these processes into three primary steps, and they are as follows;
Implementation
The first step toward bridging the gap between security and compliance is the implementation of regulations. Since technology evolves quickly, it is imperative that organizations rigorously maintain compliance with updated frameworks and increase the depth of compliance over time.
Investigation
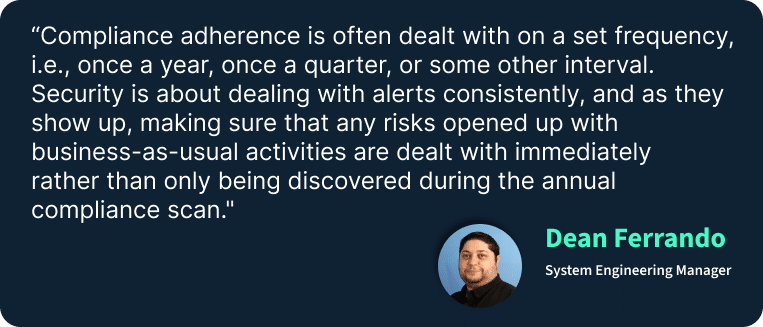
A periodic investigation is the second stage in nudging companies toward a more security-first mindset. These investigations can be annual, quarterly, or monthly, depending upon the complexity of the cloud environment, the size of the organization, and the risk management modules the firm has in place.
In the event of an attack/breach, organizations must identify and investigate thoroughly. For example, senior leaders should be held accountable if they fail to comply with mandated regulations or promote security reforms.
Improvement
The final step is closely related to these annual investigation reports. Regular feedback is one of the most overlooked components of security. It generates useful intelligence for regulators, who can compile it and utilize it to inform evolving regulatory policy. As new dangers arise, organizations can discuss mitigation measures and work on continuously improving controls for a better security posture.
Final Thoughts
After considering these viable points, we may conclude that there are far more ways to hack users and systems than ever. If you are simply concerned with compliance, you will likely always clean up after breaches rather than hunting down and stopping invaders before they can cause damage.
A clean ‘SOC 2 report’ alone will not protect you from security breaches. The paradigm must shift from guarding the network to securing the users, assets, and resources.
To learn more about risk management and security monitoring, visit us at www.scrut.io.