Conducting a SOC 2 audit is one of the best ways to evaluate security practices, but it requires a qualified professional. A SOC 2 audit should be performed by a certified public accountant (CPA) at a firm accredited by the American Institute of Certified Public Accountants (AICPA).
SOC 2 audits are no easy feat, requiring a thorough knowledge of security, privacy, and compliance requirements. The right auditor is crucial, as choosing someone unqualified can lead to delays, overlooked gaps, and inaccurate reports.
In this blog, we will explore who SOC 2 auditors are, what they do, and answer some frequently asked questions about the audit process.
Who are SOC 2 auditors?
SOC 2 auditors are licensed professionals qualified to assess whether an organization’s controls meet the Trust Services Criteria (TSC) for security, availability, confidentiality, processing integrity, and privacy.
A SOC 2 audit can only be performed by a licensed CPA firm accredited by the AICPA. Additionally, the auditor must be independent of the organization under review.
What does a SOC 2 auditor do?
A SOC 2 auditor plays a critical role in evaluating an organization’s controls against the trust services criteria, which assess key areas like security, availability, confidentiality, processing integrity, and privacy.
The auditor ensures that the organization’s practices meet the rigorous standards required for SOC 2 compliance. The role of the auditor is to examine systems, processes, and policies to provide an accurate and unbiased report on the effectiveness of the organization’s controls.
Key responsibilities of a SOC 2 auditor
1. Prepares the SOC 2 audit report
The audit report is the final deliverable of the SOC 2 audit process and typically consists of two parts: a description of the organization’s system and an auditor’s opinion on the effectiveness of controls.
This report is vital for organizations seeking to prove their security and privacy practices to clients, regulators, and other stakeholders. It serves as evidence of compliance, helping to build trust and mitigate risks related to data protection.
2. Conducts gap analysis
The auditor evaluates the organization’s existing controls and identifies any gaps in meeting the SOC 2 criteria. This involves a detailed assessment of the company’s systems and processes to ensure they are adequate in protecting sensitive information.
3. Tests controls and processes
The auditor tests the company’s implemented controls to ensure they are operating effectively. This includes testing for areas such as data encryption, access management, and incident response.
The goal is to verify that controls are not only documented but also functioning as intended to protect the organization’s data and systems.
4. Identifies areas for improvements
While performing the audit, the auditor may identify opportunities for improving security and privacy practices. These recommendations are vital for organizations looking to enhance their overall security posture and stay ahead of evolving threats.
The auditor’s insights help the organization refine its processes to ensure better compliance and stronger defenses.
Can the audit be done through an internal or external auditor?
A SOC 2 audit must be conducted by an external auditor from a licensed CPA firm. The audit requires an independent, third-party assessment to ensure objectivity and compliance with AICPA regulations.
How to become a SOC 2 auditor?
Becoming a SOC 2 auditor requires meeting specific eligibility criteria and obtaining the right certifications. The main requirement is being a certified public accountant (CPA).
In addition to a CPA license, auditors typically need experience with the AICPA’s Trust Services Criteria (TSC) and SOC 2 auditing standards. Certifications like Certified Information Systems Auditor (CISA) or Certified Information Security Manager (CISM) are also common for those looking to demonstrate expertise.
Ongoing professional development and staying current on cybersecurity and compliance trends are key to staying effective in the role.
Do I need to find different auditors in different countries?
No, you don’t necessarily need to find different auditors in different countries, as long as the auditor is qualified and familiar with the specific regulatory requirements of each country. Many audit firms have international reach and can handle SOC 2 audits for organizations operating globally.
However, in some cases, if the auditor is not familiar with local laws or regulations, it may be beneficial to work with a local firm that has expertise in the country’s specific compliance standards. The key is ensuring that the auditor understands the international scope of the audit and can provide an accurate and compliant SOC 2 report.
Can an audit firm take care of the entire SOC 2 audit process?
Yes, an audit firm can manage the entire SOC 2 audit process. Many firms offer end-to-end services, from preparing for the audit to conducting the necessary tests and producing the final report.
They can guide the organization through the audit preparation, help identify any gaps in controls, perform the necessary testing, and deliver the SOC 2 report. Working with a full-service audit firm is often advantageous because they have the expertise and resources to handle all aspects of the audit, ensuring a smooth and thorough process.
However, it’s important to ensure that the firm is independent and has the required qualifications to conduct the audit.
Which are the best audit firms for SOC 2?
Several firms specialize in SOC 2 audits, offering expertise in compliance, risk management, and security controls. Some of the well-known options include:
1. Barr Advisory: Barr Advisory supports organizations in meeting SOC 2 requirements by conducting risk assessments, developing policies and procedures, and implementing security controls aligned with the Trust Services Criteria (TSC).
2. Johanson Group LLP: This firm provides professional SOC 2 readiness assessments and helps businesses navigate the audit process to ensure a smooth compliance journey.
3. Oread Risk: Oread Risk takes a long-term approach to SOC 2 compliance, helping organizations build security frameworks tailored to their business and regulatory needs.
4. Prescient Security and Assurance: Focused on B2B SaaS companies, Prescient Assurance specializes in SOC 2 audits and offers deep expertise in cloud technologies and modern security architectures.

How much does it cost for a SOC 2 audit?
SOC 2 certification cost can vary significantly based on factors such as the type of audit, organizational complexity, and whether manual processes or automation are used.
The costs of a SOC 2 Type 1 audit typically range from $15,000 to $40,000. This audit assesses the design of controls at a specific point in time and is often quicker to complete.
A SOC 2 Type 2 audit, which evaluates both the design and operational effectiveness of controls over a period (usually 3-12 months), tends to be more expensive, ranging from $30,000 to $80,000.
These costs can increase depending on the scope, size, and complexity of your organization.
To streamline the process and reduce costs, many companies opt for automation platforms that assist with evidence collection and control monitoring, which can significantly lower internal effort and overall expenses.
How to automate the SOC 2 audit process?
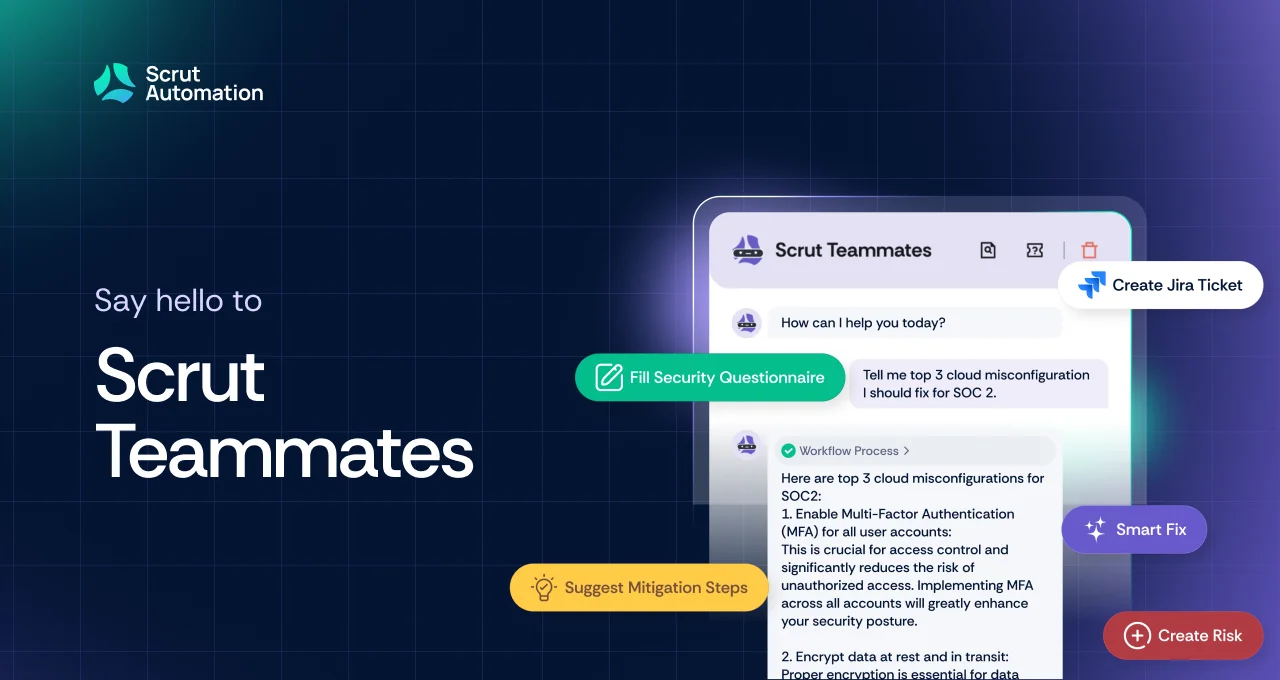
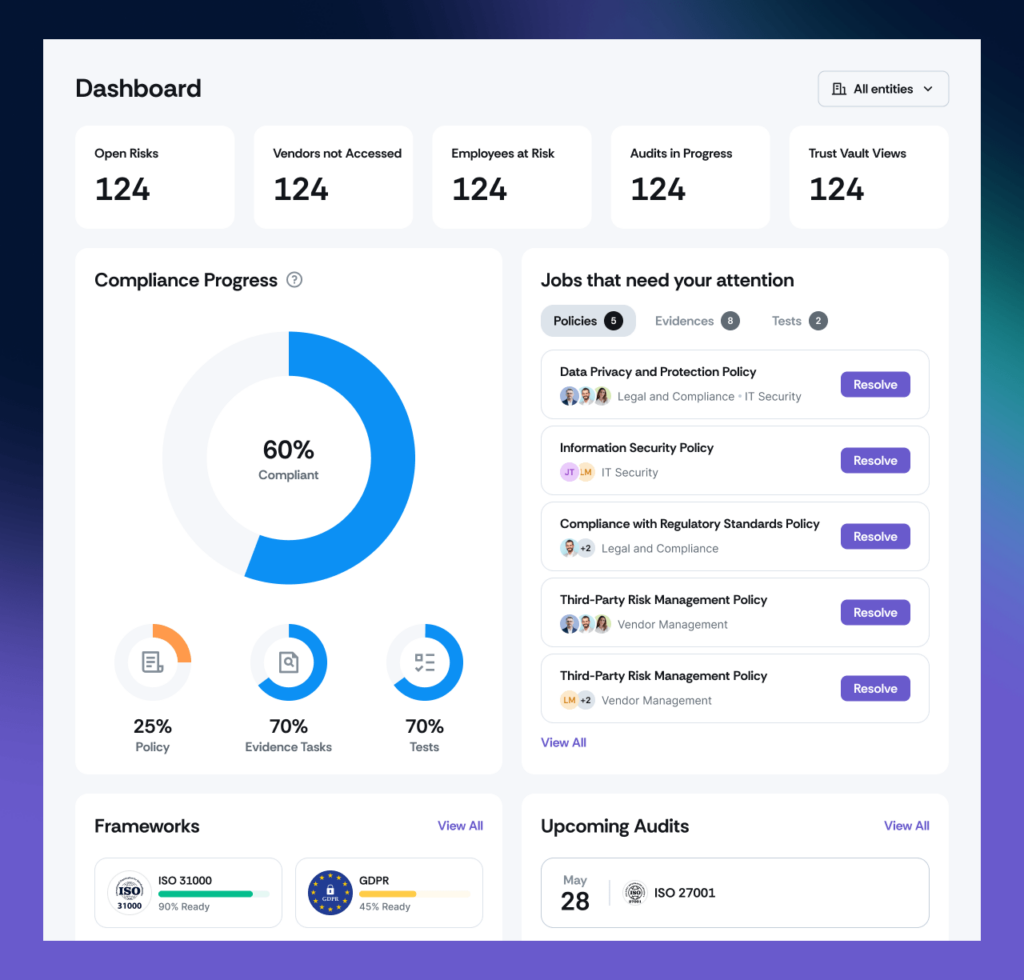
Scrut provides a comprehensive platform that automates key stages of the SOC 2 audit process, helping organizations streamline their compliance journey and reduce manual effort.
Effortless risk management
Automates the identification, assessment, and tracking of risks to align with SOC 2’s risk management framework.
Provides ready-to-use templates to document risks, assess their impact, and create mitigation strategies.
Also Read: Top 10 SOC 2 compliance software in 2025
Ready-to-use policy templates
Access a comprehensive library of customizable templates for essential SOC 2 policies, including incident response, access control, and information security.
Ensure your documentation is audit-ready while saving significant time and effort.
Simplified control management
Automatically maps your security controls to the SOC 2 Trust Services Criteria, making implementation and monitoring seamless.
Offers a centralized dashboard to track the effectiveness of controls, providing real-time compliance visibility.
Automated evidence collection
Integrates with your existing tools to automate evidence gathering for controls, reducing the burden of manual tracking and ensuring you’re always audit-ready.
Comprehensive audit preparation
Automates the identification of compliance gaps, management of non-conformities, and ensures all SOC 2 requirements are met. Facilitates collaboration between teams and auditors, streamlining the audit process.
Continuous compliance and reporting
Continuously monitors your security and privacy controls, ensuring alignment with SOC 2 requirements over time.
Generates automated reports for management reviews, performance evaluations, and audits, minimizing manual effort.
By automating the SOC 2 audit process with Scrut, organizations can accelerate their path to compliance, reduce the time spent on manual tasks, and focus on enhancing their overall security posture.

FAQs
Who can perform a SOC 2 audit?
A SOC 2 audit should be performed by a certified public accountant (CPA) at a firm accredited by the American Institute of Certified Public Accountants (AICPA).
Can an internal auditor conduct a SOC 2 audit?
No, an internal auditor typically cannot conduct a SOC 2 audit. A key requirement is auditor independence, meaning the auditor must be external to the organization. Only a qualified CPA firm can perform a SOC 2 audit.
What is the role of a SOC 2 auditor?
SOC 2 auditors are responsible for evaluating an organization’s controls against the Trust Services Criteria (TSC) for security, availability, confidentiality, processing integrity, and privacy. They prepare the SOC 2 audit report, conduct risk assessments, test controls, and offer recommendations to improve security practices.
How long does a SOC 2 audit take?
The duration of a SOC 2 audit varies based on the organization’s system complexity and the audit scope. A Type 1 audit can typically be completed within a few weeks, while a Type 2 audit usually takes at least six months, as it requires a longer observation period to assess control effectiveness over time.
Do I need to hire different auditors in different countries?
Not necessarily. Many audit firms have international reach and can conduct SOC 2 audits for global organizations. However, if an auditor is unfamiliar with local laws or regulations, it may be beneficial to work with a local firm with expertise in country-specific compliance requirements.
Can a single audit firm manage the entire SOC 2 audit process?
Yes, many audit firms offer end-to-end services for SOC 2 audits. These firms handle everything from audit preparation and gap assessments to testing and producing the final audit report. Working with a full-service audit firm can simplify the process and ensure a smooth, thorough audit.
How do I become a SOC 2 auditor?
Becoming a SOC 2 auditor typically requires certification as a CPA. Additionally, auditors should have experience with the AICPA’s Trust Services Criteria (TSC) and SOC 2 auditing standards. Certifications like Certified Information Systems Auditor (CISA) or Certified Information Security Manager (CISM) are common qualifications for SOC 2 auditors. Ongoing education is crucial to stay current with industry trends.