Now more than ever, organizations face the daunting task of protecting their information systems and data from potential breaches and vulnerabilities. This is where the Risk Management Framework (RMF) comes into play.
The Risk Management Framework, commonly referred to as RMF, is a structured approach developed by the National Institute of Standards and Technology (NIST) to help organizations manage and mitigate cybersecurity risks effectively.
By understanding and implementing RMF effectively, organizations can strengthen their cybersecurity posture, ensure regulatory compliance, and mitigate the ever-present risks of cyber threats. Meanwhile, staying ahead of regulatory requirements, such as the SEC’s new cybersecurity guidelines, is paramount for maintaining compliance and fortifying defenses against evolving threats.
In this blog, we will delve deeper into the Risk Management Framework and provide a step-by-step guide for organizations looking to successfully implement it.
Understanding the Risk Management Framework
RMF is most notably associated with the NIST Special Publication 800-37 guide, “Applying the Risk Management Framework to Federal Information Systems: A Security Life Cycle Approach.” It has been instrumental in ensuring compliance with the Federal Information Security Modernization Act (FISMA) since its introduction in 2004.
In December 2018, the RMF underwent a significant update to revision 2, reflecting the latest advancements and requirements in cybersecurity. This update was the result of a Joint Task Force Transformation Initiative Interagency Working Group, signifying the ongoing evolution of cybersecurity practices to address emerging threats.
Now, RMF is not just a recommendation but a mandate for every agency of the U.S. government, integrated into their processes and guidelines. It has also been recently incorporated into Department of Defense (DoD) instructions, underscoring its importance and relevance across various sectors.
For federal agencies, RMF serves as a comprehensive framework for securing, authorizing, and managing IT systems. It outlines a cyclical process that begins with initial system protection through Authorization to Operate (ATO) and continues with ongoing risk management through continuous monitoring.
Step-by-step guide to apply RMF

Step 1: Preparation
Introduced in Revision 2 of the Risk Management Framework, the Preparation step plays a vital role in supporting subsequent framework stages. It draws upon guidance from various NIST publications and requirements outlined by the Office of Management and Budget (OMB) policy, or a blend of both.
Often, organizations may discover that they have already incorporated certain tasks from this step into their existing risk management programs.
The overarching objective of the ‘preparation step’ is to streamline complexity in RMF implementation, align with IT modernization goals, optimize security and privacy resources, prioritize protective measures for critical assets and systems, and uphold privacy protections for individuals.
In the preparation stage of applying the Risk Management Framework (RMF), organizations should undertake several key steps to ensure a smooth and effective implementation. Here’s a step-by-step guide:
The preparation stage – Step by step

- Establish objectives: Define the overarching objectives of the RMF implementation, aligning them with the organization’s strategic goals and compliance requirements.
- Allocate resources: Allocate sufficient resources, including personnel, budget, and technology, to support the RMF process effectively.
- Identify stakeholders: Identify key stakeholders involved in the RMF process, including senior management, IT personnel, security experts, and compliance officers.
- Define scope: Clearly define the scope of the RMF implementation, outlining the systems, assets, and processes that will be subject to risk management.
- Conduct training: Provide training and awareness programs for staff involved in the RMF process to ensure they understand their roles and responsibilities.
- Develop policies and procedures: Develop comprehensive policies and procedures outlining the risk management process, including risk identification, assessment, mitigation, and monitoring.
- Select RMF framework: Select an appropriate RMF framework based on organizational needs and industry best practices, such as NIST RMF, ISO 27001, or COBIT.
- Customize templates: Customize RMF templates and documentation to suit the organization’s specific requirements and compliance standards.
- Establish baselines: Establish baselines for risk assessment criteria, including risk tolerance levels, likelihood, impact, and mitigation strategies.
- Conduct initial risk assessment: Perform an initial risk assessment to identify and prioritize potential risks to the organization’s systems and assets.
Step 2: Categorize information systems
In the journey of categorizing information systems, administrative tasks serve as the cornerstone for gaining profound insights into the organization’s architecture and functions. This step begins with delineating the boundaries of each system to understand its scope within the organizational framework.
To achieve this, organizations delve into various critical aspects such as their mission, delineated roles, and assigned responsibilities. By elucidating these fundamental components, businesses can discern the role of each information system and its significance in fulfilling organizational objectives.
An integral part of this categorization process involves examining the system’s operating environment, discerning its intended use, and understanding its interconnections with other systems. These facets provide invaluable context for accurately categorizing information systems and determining their level of importance and impact.
By comprehensively assessing these dimensions, organizations can effectively gauge the criticality of each system and prioritize resources accordingly to bolster risk management and security strategies.
Identify this information related to the organization:
- Mission
- Roles
- Responsibilities
- System’s operating environment
- Intended use
- Connections with other systems
This information influences the final security impact level assigned to the system.
Step 3: Select security controls
The selection of appropriate security controls is a critical step in the process of implementing Risk Management Framework (RMF). It determines the level of protection provided to organizational assets and information.
Security controls serve as the foundation of an organization’s cybersecurity strategy. It encompasses a range of measures designed to protect the confidentiality, integrity, and availability of its information systems and data.
Security controls are categorized into three main types: management, operational, and technical safeguards.
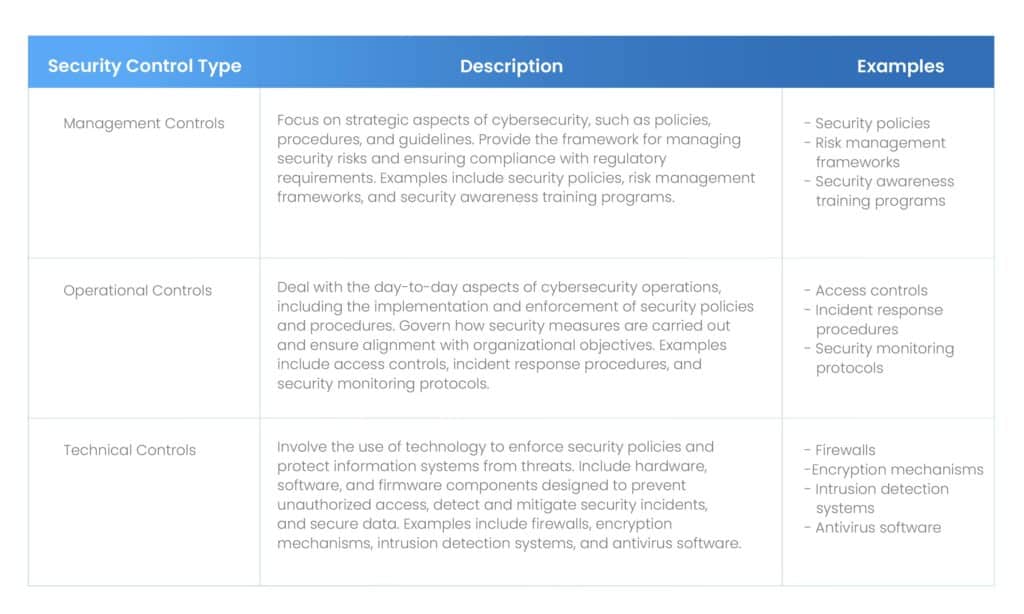
Assurance of the effectiveness of these controls is paramount. Thus, ensuring that they are not only implemented but also properly configured, monitored, and maintained to address evolving threats and vulnerabilities.
Step 4: Implement security controls
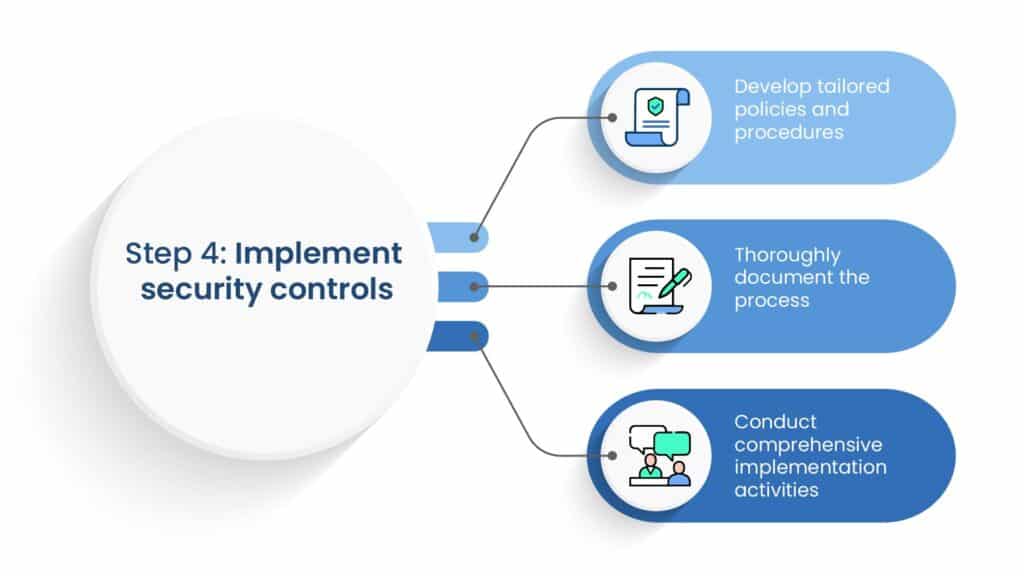
Implementing security controls involves the practical deployment and integration of these measures within the organization’s information system and operational environment. This process ensures that the selected controls are effectively applied to mitigate security risks and protect sensitive assets.
To implement security controls:
a. Develop tailored policies and procedures
- Tailored policies and procedures are created to specify the implementation and utilization of each security control within the organization’s infrastructure.
- These policies align with the organization’s security documentation requirements and are customized to suit the unique characteristics of each device or system.
b. Thoroughly document the process
- Organizations thoroughly document the implementation process to ensure clarity and consistency in applying security controls across their information systems.
- This documentation serves as a reference point for administrators. It enables them to understand and follow the prescribed procedures for implementing each control.
c. Conduct comprehensive implementation activities
- Implementing security controls involves activities beyond installing software or configuring hardware devices.
- It encompasses testing, validation, and configuration management to ensure that the controls function as intended and provide the desired level of protection.
Step 5: Assess security controls
The purpose of assessing security controls is to evaluate the effectiveness of implemented measures in mitigating security risks and protecting organizational assets.
Assessment procedures involve conducting thorough evaluations to determine whether security controls are correctly implemented. They also determine if they are operating as intended, and meeting security requirements. Assessments cover all security controls implemented within the organization’s information system, including management, operational, and technical safeguards.
Assessment criteria are established based on relevant standards and guidelines, such as those outlined in NIST Special Publication 800-53A and NISTIR 8011.
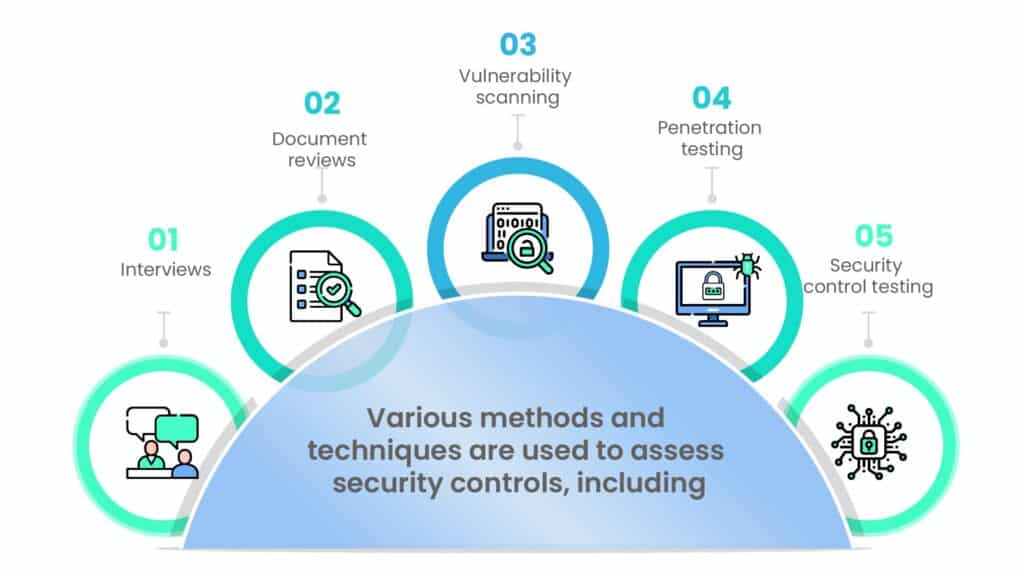
The validation process ensures that assessment results are accurate and reliable, assuring that security controls are effectively addressing identified risks.
By systematically assessing security controls, organizations can identify and address weaknesses in their cybersecurity defenses. Thus, ultimately enhancing their overall security posture and resilience against cyber threats.
Step 6: Authorize information system
Authorization of information system operation is a pivotal step based on the following steps:
- Risk assessment: A comprehensive assessment of risks associated with the system is performed. Risks are identified, analyzed, and evaluated to determine their potential impact on organizational objectives and assets.
- Risk acceptance: After assessing risks, organizational leadership must decide whether the residual risks are acceptable or require further mitigation. This involves weighing the benefits of system operation against the potential risks and making informed decisions about risk acceptance.
- Reporting mechanisms: Robust reporting mechanisms are established to communicate authorization decisions and associated risk management activities effectively. These reports provide stakeholders with insight into the security posture of the information system and ensure transparency and accountability.
- Plan of Action & Milestones (POA&M): POA&M is developed to address identified deficiencies, vulnerabilities, or areas of non-compliance with security requirements. The POA&M outlines specific actions, timelines, and responsibilities for remediation efforts to improve the system’s security posture.
- Control tracking: Comprehensive control tracking mechanisms are implemented to monitor the status and effectiveness of security controls over time. This includes tracking the implementation progress of security controls, monitoring control performance, and identifying any deviations from established security baselines.
- Status monitoring: Continuous monitoring of security controls is conducted to ensure ongoing compliance with authorization requirements. This involves collecting and analyzing security-related data, detecting anomalies or security incidents, and taking corrective action promptly.
- Authorization decision: Based on the risk assessment, acceptance of residual risks, and implementation of remediation efforts outlined in the POA&M, organizational leadership makes an informed decision to authorize the operation of the information system. This decision is documented and communicated to relevant stakeholders.
- Documentation: Authorization decisions, associated risk management activities, and control tracking efforts are documented thoroughly in authorization packages. These documents serve as evidence of compliance with regulatory requirements and organizational policies and facilitate audits and reviews.
Step 7: Monitor security controls
Organizations operate in rapidly evolving threat landscapes where new risks emerge and existing vulnerabilities evolve. Continuous monitoring enables organizations to adapt effectively, ensuring that security controls remain aligned with evolving threats.
Automated tools play a crucial role in continuous monitoring efforts.
These tools:
- Collect, analyze, and correlate security-related data from various sources
- Provide near real-time insights into security events, configuration changes, and potential security incidents.
- Enhance risk management by enabling organizations to identify and assess security risks more efficiently.
- Help minimize the impact of security incidents
- Help reduce the likelihood of successful cyber attacks.
In conclusion
In summary, the RMF standardizes controls, language, and improves reciprocity across government agencies. It prioritizes risk over uniform solutions, integrates security into systems, and expedites security responses.
Continuous monitoring enhances federal agency cybersecurity, facilitating comprehensive reporting and risk management.
Implement continuous monitoring with Scrut to enhance your organization’s cybersecurity posture and ensure ongoing compliance with regulatory requirements. Scrut provides advanced automated monitoring tools that offer near real-time insights into security events. Thus, enabling prompt response to emerging threats and vulnerabilities. Get in touch today!
Frequently Asked Questions
The RMF is a structured process that helps organizations identify, assess, and mitigate risks to their information systems and data. It provides a framework for managing cybersecurity risks effectively, ensuring the confidentiality, integrity, and availability of information assets. RMF is crucial for organizations, as it helps them establish a proactive approach to cybersecurity and comply with regulatory requirements.
Unlike some other risk management frameworks that focus solely on information security, the RMF takes a broader approach by integrating security into the entire system development lifecycle. It emphasizes continuous monitoring and ongoing assessment of security controls, ensuring that organizations can adapt to evolving threats and vulnerabilities effectively.
The key steps in implementing the RMF include categorizing information systems, selecting appropriate security controls, implementing those controls, assessing their effectiveness, authorizing system operation, and monitoring security controls continuously. These steps ensure that organizations can systematically manage and mitigate cybersecurity risks across their information systems.
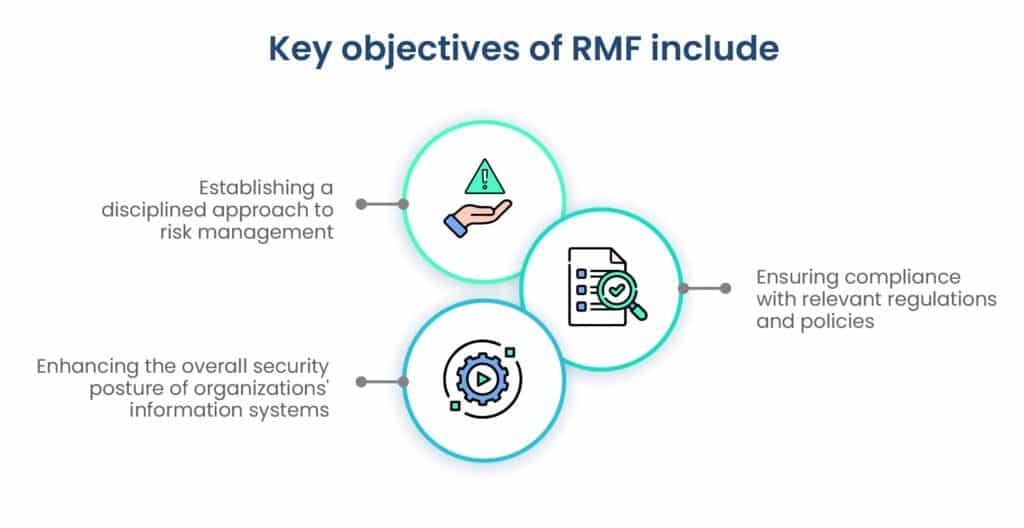
The primary objectives of the RMF are to establish a disciplined and structured approach to managing cybersecurity risks, ensure compliance with relevant laws, regulations, and policies, and enhance the overall security posture of organizations’ information systems. By following the RMF, organizations can identify, prioritize, and address security risks effectively.
The RMF helps organizations manage cybersecurity risks effectively by providing a systematic and repeatable process for identifying, assessing, and mitigating risks. It ensures that security controls are implemented based on risk assessments and continuously monitored to address emerging threats and vulnerabilities. Additionally, the RMF promotes a culture of security awareness and accountability throughout the organization, enhancing its overall resilience to cyber threats.